Phishing has long been one of the simplest and most effective ways for cybercriminals to gain access to sensitive information. But what was once a manual, opportunistic crime has now scaled into a professionalized business model.
With AI in the mix, phishing attacks are harder than ever to detect. Phishing-as-a-Service (PhaaS) gives hackers and scammers the tools, infrastructure, and even customer support to launch large-scale, highly convincing campaigns at minimal cost. For executives, this shift represents a significant and growing threat to enterprise security, with implications that extend well beyond IT.
Why Executives Should Care
Phishing is no longer just an inconvenience for employees or a technical headache for security teams—it’s the gateway to a far more devastating threat: ransomware. Statistics show that 54% of all ransomware attacks begin with a phishing email. Your defense against such an extortion malware attack is a defense against the other.
Through PhaaS, cybercriminals have industrialized the process, turning it into a subscription-based economy that mirrors legitimate cloud-based platforms. This lowers the barrier to entry, allowing virtually anyone to launch sophisticated phishing campaigns. The business risks are wide-ranging:
1. Financial Losses
PhaaS campaigns frequently target login credentials, credit card details, and bank accounts. A single successful attack can lead to significant direct financial losses, and the financial impact of a successful phishing attack is going up.
The average cost of a data breach that originated from phishing has climbed to $4.88 million in 2024, a nearly 10% jump from the previous year. This figure represents not just stolen data, but also the costs of operational disruption, fines, and so on. It does not include reputational damage and other downstream effects.
Beyond immediate theft, attackers may also use stolen data to fuel ransomware attacks, where businesses are forced to pay large sums to restore access to their systems.
2. Reputational Damage
When customer or employee data—such as social security numbers, phone numbers, or credit card details—is exposed, the reputational fallout can be long-lasting.
Clients and partners begin to question whether the organization can protect sensitive information. For executives, reputational harm is often harder to recover from than the financial loss itself.
3. Operational Disruption
Phishing often serves as the entry point for broader cyberattacks. Once attackers gain access through stolen login credentials, they can deploy malware, malicious scripts, or even launch extortion malware attacks that halt business operations.
Delivery timelines, customer commitments, and internal productivity all suffer.
4. Pressure on Security Teams
PhaaS significantly increases the volume and sophistication of attacks. Even well-resourced but overstretched security teams struggle to keep up.
This creates gaps that cybercriminals exploit, raising the organization’s overall cyber risk profile.
How Phishing-as-a-Service Works
At its core, PhaaS mirrors the “as a service” model that has transformed legitimate software businesses.
Just as Software-as-a-Service makes enterprise applications easier to deploy, providers of PhaaS services provide online attackers with ready-made phishing kits, email templates, and hosting infrastructure.
Turnkey Access for Cybercriminals
A subscription to a PhaaS platform gives attackers access to everything they need: malicious email templates, phishing pages that mimic legitimate services, hosting on cloud-based platforms, and even technical support.
The kits are so polished that attackers with little or no technical skill can immediately begin launching phishing campaigns.
Inside a Modern Campaign
A typical phishing attempt begins with a lure—usually a malicious email, text message, or increasingly, a QR code embedded in a message. The communication looks authentic, often copying the design of a legitimate service like a financial institution or Microsoft. While professional branding and convincing language are common, small giveaways such as spelling errors or awkward phrasing may still appear.
The malicious email typically directs the victim to a fake website. These phishing pages closely mirror legitimate login pages, tricking victims into entering their credentials. Once victims authenticate, the information is instantly harvested and transmitted to the attacker. Some PhaaS vendors even use a Telegram bot or Telegram group to notify attackers in real time when stolen data is captured.
Beyond credential theft, phishing kits can also deploy malware, deliver malicious attachments, or use malicious links to redirect traffic. Some campaigns are designed to harvest credit card details or sensitive data like social security numbers, while others enable broader attacks.
Why the Threat Is Growing
Several dynamics make PhaaS particularly concerning for enterprise leaders:
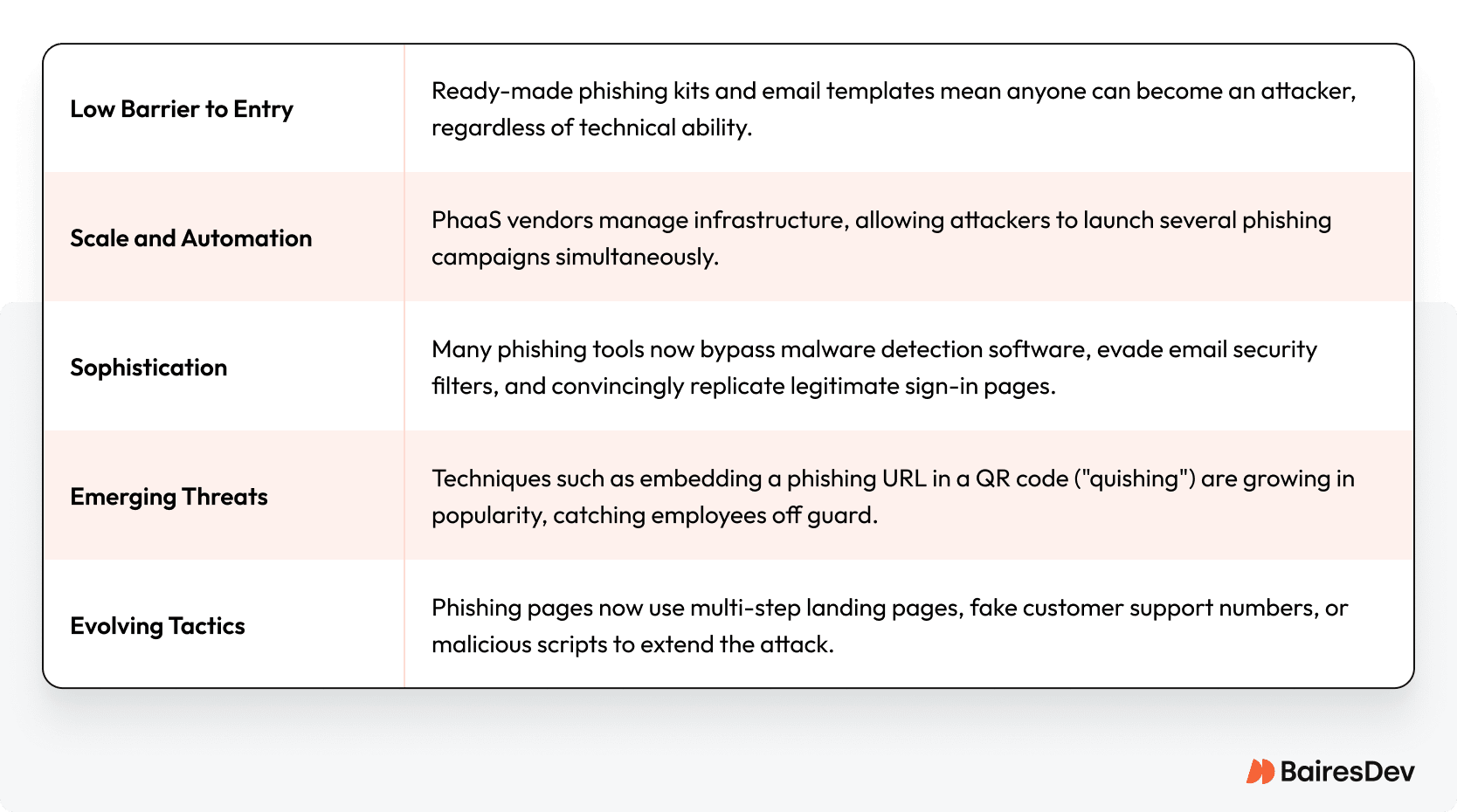
The result is that most attacks today are no longer opportunistic, but orchestrated with professional precision. For enterprises, this means exposure to a steady stream of highly targeted phishing, many of which slip past traditional defenses.
Building a Defense Strategy
Defending against phishing is not about a single tool or policy—it requires a layered approach that combines human vigilance with robust technical controls. Executives play a key role in ensuring these defenses are resourced and prioritized.
The Human Firewall: Security Awareness Training
Employees remain the first line of defense. Without proper training, even the most advanced technology cannot prevent mistakes. Regular education in cybersecurity and ongoing phishing simulations help employees recognize threats.
- Education: Provide detailed instructions on how to detect malicious emails. Teach staff to check sender addresses, hover over links, and be wary of urgent requests for sensitive information.
- Simulation: Conduct controlled phishing within the organization to measure awareness and identify departments most at risk.
- Reporting culture: Encourage employees to report suspicious emails without fear of reprimand. This feedback loop strengthens email security across the organization.
The Technological Shield: Layered Security
Technology must complement human awareness. Key measures include:
- Multi-Factor Authentication (MFA): Two-factor or multi-factor authentication significantly reduces the success of credential theft. Even if attackers steal a user’s credentials, a second verification step blocks access.
- Anti-Phishing Software: Deploy advanced malware detection software integrated with your email security system. Modern platforms use AI to detect malicious attachments, phishing links, and unusual login patterns.
- Email Security Gateways: Enterprise-grade gateways—such as Microsoft Defender for Office 365—scan emails for malicious hyperlinks, phishing URLs, and impersonation attempts. Features like SafeLink can help protect users at the moment they click.
- DNS and IP Filtering: Proactive filtering prevents employees from accessing known malicious websites or phishing pages, reducing exposure.
- Incident Response Preparedness: Ensure security teams at capacity have playbooks to respond quickly when phishing attempts succeed.
A Continuous Executive Imperative
Phishing-as-a-Service has transformed cybercrime into a business.
Threat actors evolve their tactics constantly, from exploiting fake websites and malicious links to experimenting with new methods like QR code phishing. For enterprises, protecting against these attacks is not a one-time IT project—it’s an ongoing imperative.
Executives must recognize phishing as both a cybersecurity and a business risk. By investing in layered defenses, prioritizing employee cybersecurity education, and ensuring continuous monitoring, organizations can significantly reduce their exposure to phishing attempts. Staying informed and proactive is the only sustainable strategy.
Frequently Asked Questions
What is the difference between phishing and PhaaS?
Phishing is an attack where malicious actors trick victims into revealing sensitive information. Phishing-as-a-Service (PhaaS) is the subscription model that sells phishing tools, hosting, and support to other criminals, enabling them to launch phishing campaigns at scale.
How does phishing typically work in a PhaaS model?
Attackers purchase access to a PhaaS platform, use email templates or ready made phishing kits to lure victims, and deploy fake login pages. Once victims enter credentials or sensitive data, the information is sent to the attackers, often in real time.
What should executives prioritize to protect organizations?
Leadership should fund and enforce multi-factor authentication, invest in anti-phishing software, and mandate recurring security awareness training. They should also ensure strained security teams have resources to detect and respond quickly to phishing attempts.
Can multi-factor authentication stop all phishing attacks?
MFA is highly effective but not foolproof. Some sophisticated techniques can bypass MFA, and it doesn’t protect against all malicious attachments or ransomware attacks. MFA should be part of a broader defense strategy.
How do phishing campaigns exploit QR codes?
Some phishing emails now use a QR code to deliver a phishing URL. When scanned, the code redirects the victim to a fake login page or malware download. This tactic bypasses traditional email scanning tools and has become an emerging threat.
Why is PhaaS considered a growing threat for enterprises?
Because it lowers barriers for attackers, enabling more phishing attempts at scale. PhaaS vendors continually evolve their tools to evade detection, increasing the pressure on enterprises to keep pace.
What role should executives play in combating phishing?
Executives must treat phishing not just as an IT concern but as a board-level risk. By framing phishing defense as part of enterprise risk management, they can align budgets, prioritize resources, and hold teams accountable for results.






