Modern enterprises are changing fast—cloud services, SaaS adoption, and distributed workforces have eroded the traditional idea of a secure, internal network. In this borderless context, relying on a trusted perimeter is no longer effective. Zero Trust Security offers a more resilient model: verify every access request based on identity and context, not location.
This article addresses how technology leaders (CTOs, VPs of Engineering, Head of Security) can architect, adopt, and operationalize Zero Trust in a way that balances risk reduction with business agility.
Why Zero Trust Is Now Strategic, Not Optional
Zero Trust is no longer a niche security concept — it’s a strategic imperative. As hybrid work, cloud sprawl, and evolving threats reshape the enterprise perimeter, organizations are adopting Zero Trust to enforce least-privilege access, reduce breach impact, and align security with modern delivery models.
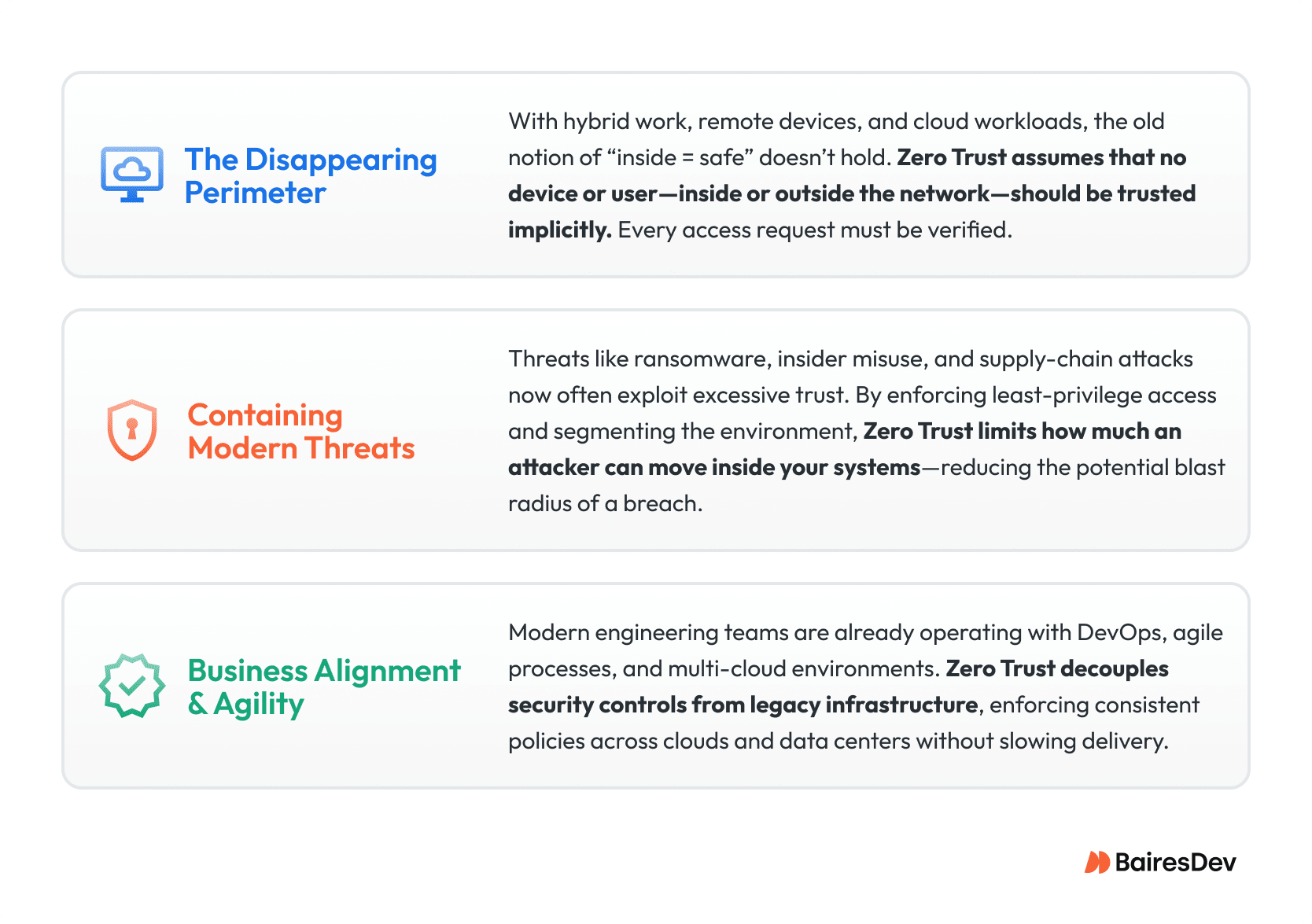
Plus, many leaders see this as a long-term business enabler—not just a security cost. Investments in identity controls, microsegmentation, and telemetry can also improve onboarding speed, simplify access for staff augmentation teams, and streamline operations.
Core Principles of Zero Trust Architecture
Identity-First Verification
Identity becomes the control plane. Access requests must be continuously authenticated—using strong MFA and Single Sign-On (SSO)—and evaluated against adaptive risk signals, such as:
- Role and user identity
- Device posture (patch level, encryption, OS)
- Contextual factors (time, location, behavior)
These checks ensure that trust is never assumed.
Least Privilege Access
Grant only the minimal permissions that a user or workload needs—and make those permissions temporary (“just-in-time”). This reduces the pathways an attacker could exploit after compromising an identity.
Microsegmentation & ZTNA
Partition your network into smaller segments, isolating workloads, applications, or functions. Use Zero Trust Network Access (ZTNA) to replace legacy VPNs: instead of broad network connections, ZTNA broker provides a one-to-one, context-aware path to a specific application, without exposing the full network.
Pervasive Telemetry & Continuous Monitoring
Visibility is essential. Aggregate logs, telemetry, and identity data across endpoints, network flows, and cloud services. Apply behavioral analytics and threat intelligence to continuously evaluate risk—and update policies dynamically as risk changes.
A Practical Roadmap to Zero Trust Adoption
Implementing Zero Trust isn’t a one-off—it’s a phased, multi-year journey. Here’s a constructive roadmap for enterprise leaders:
Phase 1: Assessment & Identity Modernization
- Inventory & Map: Catalog users, devices, applications, data flows, and existing security controls.
- Strengthen Identity Layer: Deploy MFA and centralize IAM (Identity & Access Management) as a single source of truth for all access policies.
Phase 2: Protect High-Value Resources
- Deploy ZTNA: Replace legacy VPNs with a brokered access model to limit network exposure.
- Segment Strategically: Begin microsegmenting the highest-risk applications and sensitive workloads first. This gives meaningful risk reduction without requiring a full rearchitecture up-front.
Here is a comparison that clarifies how traditional models differ from a Zero Trust approach:
| Feature | Legacy Security | Zero Trust Architecture |
| Trust Basis | Implicit trust inside traditional perimeter | No implicit trust—verify every request |
| Access Control | Broad, network-level (e.g., VPN gives subnet access) | Identity- and context-driven, granular least-privilege |
| Visibility | Siloed logging, limited lateral movement insight | Centralized telemetry, continuous risk scoring |
| Core Technology | Firewalls, perimeter defenses | ZTNA, microsegmentation, IAM, secure gateways |
Phase 3: Build the Zero Trust Enterprise
- Deep Microsegmentation: Enforce identity-based policies for every workload, both on-prem and cloud.
- Automate & Orchestrate: Integrate Zero Trust into DevOps pipelines. Use orchestration tools to automate policy enforcement and threat response, revoking access in real time as risk evolves.
Architectural Shift: From VPN to ZTNA
From an engineering perspective, the most visible change is often migrating from VPNs to ZTNA. Traditional VPNs grant broad network access—meaning a compromised credential could let an attacker roam freely.
In contrast, ZTNA brokers connections at the application level. The user never gains full network access; instead, they connect only to specific applications they are authorized for. This enforces least privilege by default and reduces the attack surface.
Secure web gateways and adaptive firewalls become enforcement points—dynamically evaluating sessions according to Zero Trust principles.
Why Zero Trust Supports Velocity & Talent
For engineering leaders focused on delivery and resource constraints, Zero Trust offers long-term value beyond risk reduction:
- Reduced Risk = Faster Execution: With fine-grained access and microsegmentation, you minimize the risk of a breach derailing large projects.
- Accelerated Onboarding: New employees or outsourced engineers can be granted precise access via ZTNA—no more broad VPN access, and no time wasted on legacy network configurations.
- Operational Efficiency: By standardizing on MFA, ZTNA, and centralized IAM, you free up your security team to focus on high-value initiatives instead of managing VPN configurations or firewall rules.
Real-World Impact: Why Leaders Are Taking Notice
- An IBM report found that breach costs are surging: the average cost of a data breach reached $4.88 million in 2024, up 10% year over year.
- According to NIST, Zero Trust architecture is increasingly adopted as a response to hybrid work, cloud-first environments, and remote devices—all of which erode traditional perimeters.
These metrics show not just risk, but also the urgency and ROI of shifting to a Zero Trust model.
Getting Started—Practical Tips for Engineering Leadership
- Align Zero Trust with business priorities: Frame your roadmap in terms of risk reduction, improved onboarding, and operational efficiency—not just security.
- Start small, scale smart: Tackle identity and access first, then move into high-risk segmentation. Quick wins help justify further investment.
- Integrate with DevOps: Embed security policies into your CI/CD pipeline so that Zero Trust enforcement happens continuously, not just at deployment.
- Measure and evolve: Use telemetry to monitor how access is used, where risk is highest, and how your policies are performing. Be ready to tune dynamically.
The Trust That Always Gets Verified
Zero Trust isn’t just a security program—it’s an architectural shift. By centering on identity, context, and least privilege, you rebuild trust on your terms, not the attacker’s. For a scaling enterprise, that means more agility, lower risk, and a security model that supports rapid growth—not slows it down.






