When we first began talking about Zero Trust, the focus was eliminating implicit trust at the network perimeter. Today, the conversation has shifted from, “Do we have Zero Trust?” to “Why hasn’t it scaled?” The data reflects that tension: 82% of organizations say Universal Zero Trust Network Access (ZTNA) is essential to their security strategy. Yet according to the same survey, only 17% have fully implemented it.
As AI becomes embedded in enterprise infrastructure, new attack patterns are emerging, and one-time authentication is no longer a durable trust signal. At the same time, we are also operating in an environment where machine identities like bots, APIs, IoT sensors, and AI agents already outnumber human users. Traditional “authenticate once and trust the session” models don’t hold anymore.
Zero Trust 2.0 replaces static verification with continuous validation, and perimeter thinking with identity resilience. In our webinar, Welcome to Zero Trust 2.0 & Identity Security, Zero Trust creator John Kindervag, Office of CTO at Cisco Dr. Kapil Bakshi, and Director of SLED Strategy at Iron Bow Technologies and former U.S. House CIO Nelson Moe joined me to explore what this shift actually means for security leaders and why scaling identity security is now a business resilience mandate.
Zero Trust 2.0 Is Identity Resilience
Zero Trust 2.0 begins with a reframing of how organizations are prepared to scale identity as the foundation of their security strategy. While the term “Zero Trust 2.0” has emerged in industry discussions, Kindervag emphasized that what’s actually evolved is *awareness*, not the underlying principles. As creator of Zero Trust, he reminded us of the 5 steps for this security practice.
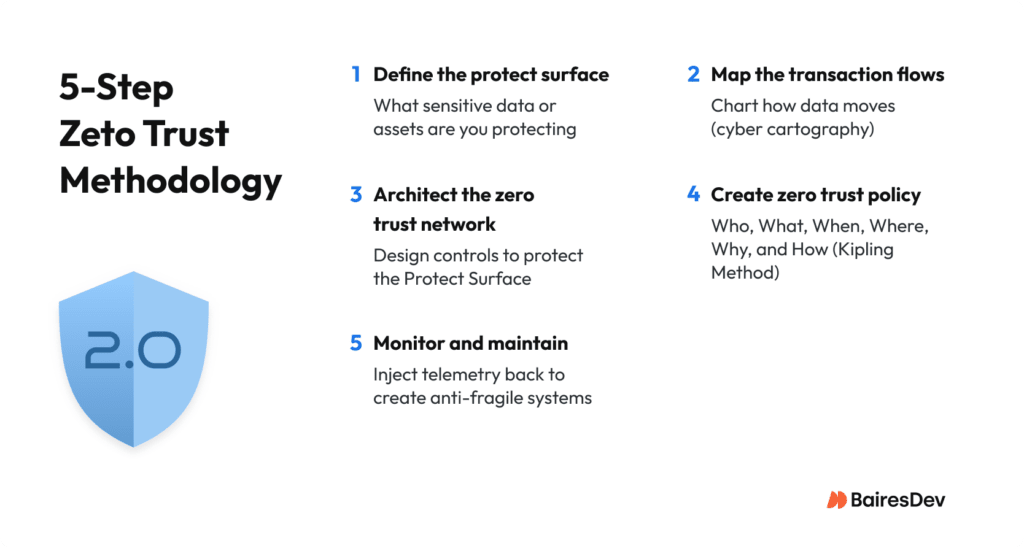
Kindervag’s guidance for organizations evaluating Zero Trust was unequivocal: “Don’t worry about the technology until you figure out what you want to use the technology for.” Skipping this step defeats any well-intentioned implementation of Zero Trust, just as thinking that it can be treated as a product you buy, rather than an architectural discipline you must implement and enforce.
Dr. Bakshi reinforced this strategic reframing, adding that “we’re in major flux in the tech industry, and identity and zero trust is a central piece of doing that.” His observation underscores how Zero Trust has moved from an isolated security initiative to a fundamental enabler for digital transformation, particularly as organizations navigate hybrid cloud, SaaS proliferation, and AI-enabled automation.
What has fundamentally changed is the shift from Zero Trust as a “one-time gate check at the border” to continuous trust assessment throughout user and system sessions.
The challenge, Bakshi noted, is operationalizing this shift without breaking business operations. “The fear of breaking the business with false positives” creates a difficult balancing act: set risk policies too tight and legitimate traffic gets blocked; set them too loose and attackers slip through. His recommendation: leverage AI-native segmentation to dynamically calibrate signal-to-noise ratios based on actual behavior patterns, not static thresholds.
Identity as Living State, Not Just a Gate
Identity, Kindervag argued, isn’t about humans on networks—it’s about machines asserting human origin. The problem is that organizations treat these assertions as facts rather than claims requiring continuous validation. This reframing shifts focus from who logged in to what those credentials are doing post-authentication. “We take identity as a singular data point, and we make an access control decision based upon one piece of data,” Kindervag explained. “That piece of data does not have enough context to determine whether to allow or deny.”
From his government experience, Moe extended that risk beyond internal users. Third-party and outside-system connections, he noted, are often the weakest link. The real question is which external systems interact with your environment without giving you full visibility or control.
Bakshi reinforced this: “Identity is no longer a gate. It’s a living state.” Organizations must assume identities are compromised by default and validate behavior continuously, especially as non-human identities now outnumber humans 10-to-1 in cloud environments. Moe added a practical warning: MFA remains a “single spot” check. Once an account is compromised, attackers can “live off the land,” using legitimate internal tools unless behavior is re-verified throughout the session.
Bad Policy Is The Number 1 Risk
Both Kindervag and Bakshi converged on the same diagnosis for failure: policy fragmentation is the real vulnerability, not technology gaps. Kindervag stated that “100% of successful cyberattacks are bad policy, not bad controls, not bad product choices,” sharing an anecdote about a global bank’s firewall with its first rule set to ‘any, any allow’—allowing all traffic from any source to any destination—effectively disabling all protections.
Bakshi highlighted the challenge: “Policy is fragmented or siloed—policy in cloud, policy in data center, policy for SaaS, policy for branches. Can we pull them together into a universal policy?” Unified policy, he noted, is “easier said than done” but essential for least-privilege access everywhere.
The Real Implementation Challenge Is Friction, and It Has to Be Engineered
One audience question cut to the operational reality: “How do you deal with user friction and continuous interruption?” The question exposes Zero Trust’s central implementation tension: poorly designed controls don’t just annoy users; they create security vulnerabilities when users find workarounds.
Design Friction Strategically, Don’t Eliminate It
Bakshi reframed friction as a design choice, not an inevitable cost. “Teams struggle when they rely on active friction, like passwords, MFAs, prompts, instead of passive friction like device postures and biometrics,” he explained. “Security should be invisible to the user until they do something risky.”
The principle is to reserve interruptions for high-stakes moments. For routine operations, validate continuously in the background. “Force users to jump through hoops for low-risk tasks, and they will find ways around it, creating even more vulnerabilities.”
Map Flows Before Enforcing Policy
Another question that arose was whether high friction indicates poor transaction mapping. Nelson Moe noted that ‘high friction’ isn’t only technical. It can reflect an organization’s risk acceptance model and culture, especially in environments where people are structurally disincentivized to take on risk. At the design level, excessive prompts are a signal of incomplete mapping where roles weren’t defined, flows weren’t understood, or policies were applied universally instead of contextually.
Kindervag reinforced this: “If you don’t understand the flows, you can’t understand where the friction is coming from.” Moe’s practitioner guidance was direct: “Start with understanding the business flows… how does this department actually do their work?” Map business outcomes and traffic patterns first, then layer in controls.
Moe also highlighted organizational friction. Teams often have limited time to justify Zero Trust to leadership. His advice is to explain the “why” upward and involve users early. Set expectations about disruption and align on the broader goal. Zero Trust takes time, and success depends on clear communication about business resilience.
Zero Trust Has a People Problem Too: Turnover
Turnover among security professionals poses a maturity test. I asked the panel: “What is the impact of team turnover on security? Are companies ready for it?” The answer exposed a maturity gap. Bakshi emphasized that, “HR policies for exiting team members must align with identity systems in an automated fashion.” Manual offboarding creates vulnerabilities.
Kindervag provided proof, citing a case where someone retained access to a large organization’s internal networks for three years after leaving because no one disabled the account. He noted that even today, organizations still don’t do enough on this front.
The operational fix requires two disciplines:
- Automate the identity lifecycle. Tie access provisioning and deprovisioning directly to HR systems. Don’t rely on manual processes.
- Validate continuously. Continuously check whether all identities are still valid, invalid, or stale. When roles change, redefine what those identities should access.
Kindervag identified the core policy gap: organizations have rigorous processes for granting access but rarely audit what should be revoked. Access accumulates over time, creating compounding risk. Turnover management is a Zero Trust maturity indicator. Handle it cleanly to avoid failing quietly through orphaned permissions.
Scaling Zero Trust in Motion
Zero Trust 2.0 is about scaling identity governance under constant change. The challenge now is operationalizing them correctly. Success requires mapped transaction flows before enforcement, passive friction over active interruptions, unified policy across environments, and continuous validation. As Kindervag emphasized, start with defining what you’re protecting, not what products to buy.
The threat landscape is accelerating as autonomous systems operate at machine speed. Prepare your organization to operationalize identity with discipline and align security to business reality. As Moe framed it, Zero Trust is a journey requiring evolutionary progress. Click here to watch the full webinar and if you’re ready to start your security journey, contact our team. We’re ready to help.






