cybersecurity
(63)Open-source projects have been powering our software for a long time, but can their open nature pose a risk for us?

By Rocío Belfiore
6 min read
Remote work is here to stay, and companies must ensure their distributed networks are secure against rising cyber threats from outside and inside their borders.
By David Russo
6 min read
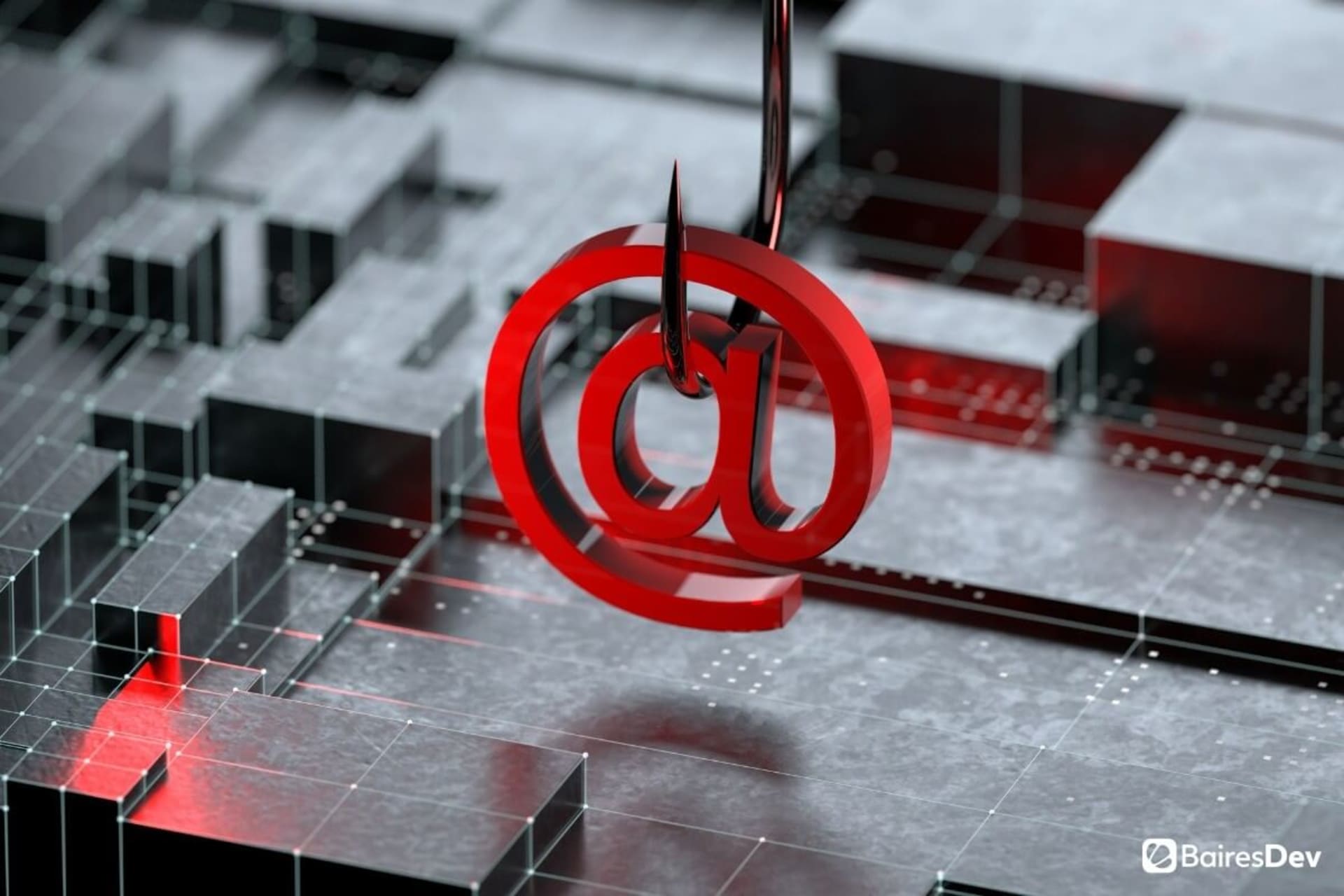
We’re living in a world where phishing is a palpable and ubiquitous phenomenon, so it’s better if we understand what it’s all about.

By James Miller
7 min read
Building your projects with security in mind leads to better and more secure software, preventing possible leaks and breaches that might damage your business.

By Facundo Molina
6 min read
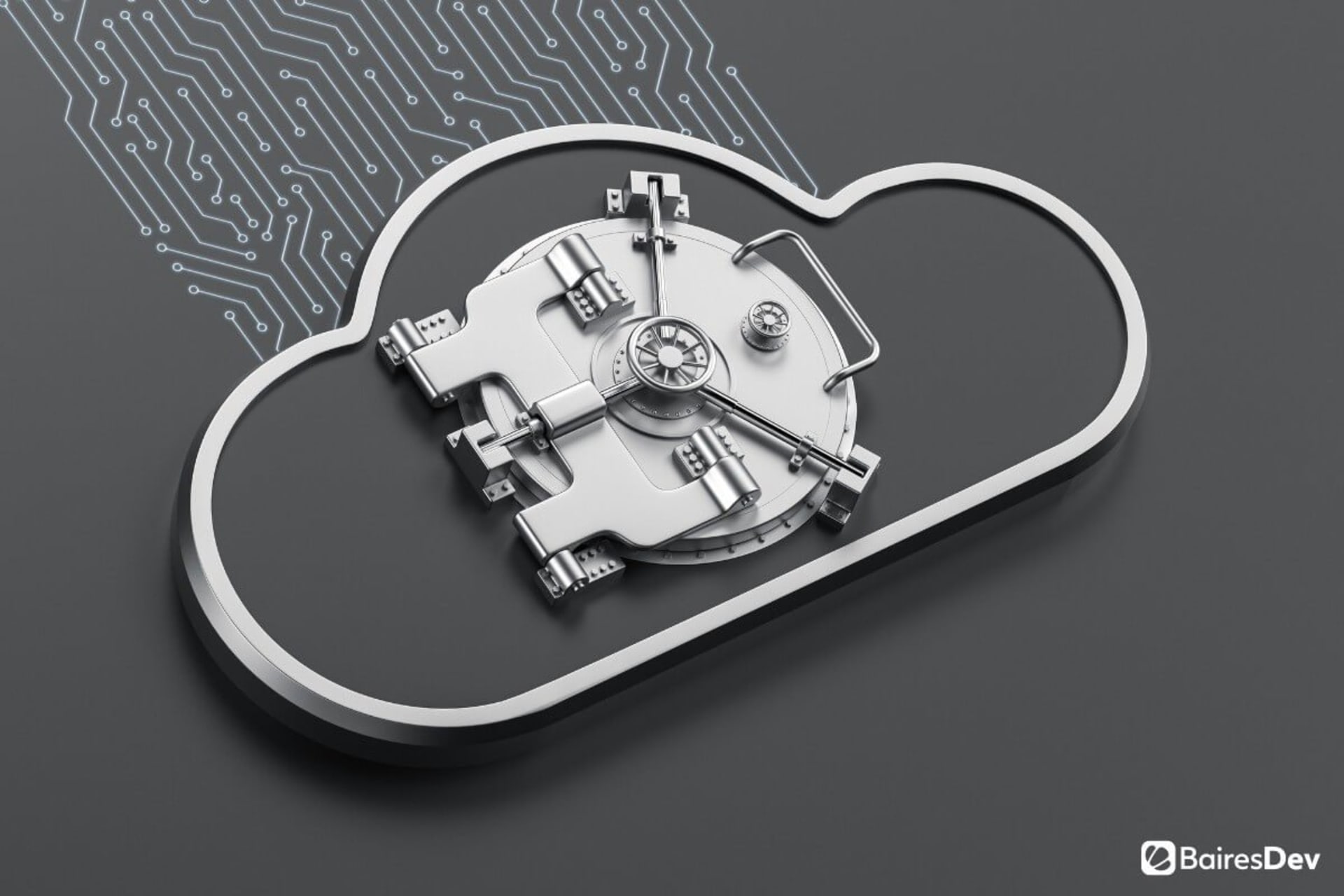
Here we explore the reasons cloud services are being exploited, how it’s happening, and what you can do to prevent it.

By Lorena Albaretto
6 min read
The number of cyber threats that could potentially harm your company can be daunting. Fortunately, there are many ways you can stay safe.

By Lisandro Pavetti
6 min read
As remote work standardizes among companies from different industries, it’s important we don’t forget about cybersecurity for remote teams.
By Brandon Roberts
5 min read
When it comes to cybersecurity, prevention is key. And yes, the costs go way beyond monetary expenses.

By Edward Batten
6 min read
Strong cybersecurity measures are like insurance: it’s better to have it and not need it than to need it and not have it.

By Facundo Molina
6 min read
Is your company prepared for a cyberattack? If you think the answer is yes, consider all that’s happened in the past few months.

By Facundo Molina
6 min read
Passwords are still heavily in use but are gradually becoming less prevalent as authentication methods that are newer, more convenient, and more secure emerge.

By Edward Batten
6 min read
The increase in work-from-home (WFH) arrangements — and the weaker security inherent in those external connections — provides additional attack vectors for cybercriminals to access companies.

By James Miller
6 min read
It's time to take the first step towards autonomous endpoint security.

By Jeff Moore
7 min read
Rain or shine, cybercriminals are always on the prowl. And with the Coronavirus Pandemic forcing all types of companies outside their comfort zone, cybersecurity issues can quickly take anyone by surprise. No matter what industry you work on or how successful your business is, the circumstances have changed—which means your approach to cybersecurity must change [...]

By Richard Kaplan
5 min read
Financial services enterprises fall victim to cybersecurity attacks 300 times more often than businesses in other industries...

By Jason Walsh
6 min read